CyberYozh security group is a project set up by an international company that offers internet security services. They are driven by the development of IT security software and awareness and training for users.
CyberYozh security group offers security software, get help with protecting your data and publish for free very interesting articles in Internet Privacy and Security course, that are very easy and exciting written. All aspects and details are described in detail, therefore, it can be understood by anyone who has read, even if you have any knowledge in security area. Chapter after chapter, you will dive into the basics of security and anonymity of you online.
In the today's world, everybody needs to know how to remove information on their activities, e.g. clean up the system’s registry, list of recently used applications, etc.
What this course about
The idea to analyze Internet traffics of users for forensic purposes, cyber spying or advertising revenue is gaining ground every year. You are going to learn how to protect yourself from DIP techniques as well as other threats.
This book's objectives are modest and practical: to teach you to protect yourself from cyber espionage, get round unlawful censoring and suppressing of resources, safely protect your electronic data, and remain anonymous in the Internet.
A substantial part of this book will address protection from a variety of intrusions into your private life, ways to stop any attempts to follow your activities on the Internet, or get access to your communication and e-mails. It is no less important to hide your actual location, prevent illegal access to your web-cam and microphone so as to monitor your actions through those.
You will thoroughly explained IP, DNS, MAC address, browser fingerprint, browser cache, and other notions important for your anonymity and safety.
While reading this online book, you will find:
- real life examples
- hackers stories
- useful hints
- advices to stay anonymous while using internet
It is also important to note that this is the first high quality resource available in Russian.
Why it is important to be informed
Most hackers attacks are mass and non targeted. Hackers infect anyone who may get unlucky, they don't care about your social status, financial situation, or stance on government policies.
Unfortunately, antiviruses can protect you only from a small number of threats.
Without any doubt, your money is the most desired loot for a hacker if you don't use online payment systems like PayPal, e-banks or Bitcoin. Your data can be simply locked up and held for ransom a hacker can steal your email accounts, social network accounts, accounts with eBay Amazon Aliexpress and other popular sites and then sell them off in a lucrative deal on the darknet. They are subsequently used in spam, carting and fraud activity. Your computer can be used as a proxy server for anonymous illegal action, spam sending, infecting other computers, launching DDoS attacks, breaching companies and government organizations and may lead to dire consequences. Don't fall victim to misconceptions set up comprehensive internet privacy and security.
Why should you need privacy and security on the Internet?
Fine for downloading a file from the Internet
Many of you would say to yourself that you don't share anything, you just download. But you will be disappointed, not only people who share files are subject to persecution, those who distribute them also face huge damages. You know that torrent clients (same uTorrent) start automatically distributing downloaded files making you a criminal.
Being watched by special agencies
According to the documents shared by Edward Snowden, the US special agencies watched over a million citizens of Brazil. Such mass surveillance and data collection constitute direct interference with citizens' private life and take place all over the world. Why should you think you are not being watched too? Perhaps it's time to stop relying on your luck and start thinking about Internet privacy and security? This is not a paranoia, this is an adequate response to the data mining activities of special services, primarily from the US.
Do you still believe that special agencies are not watching you? Then visit the site wikileaks.org. It is known that the visitors of this website are closely watched by special services, and this was confirmed by Edward Snowden. Wikileaks is not the only site watched by special services. For instance, a popular torrent site Pirate Bay is also under surveillance.
Censorship
It is absolutely clear why drug dealing websites or child pornography should be blocked, but the government of many different countries blocks the websites of opposition editions, politicians' blogs depriving us of the right to hear other viewpoints.
Censorship is not just a tool that restrains common users, it's a proven method of exerting pressure on individuals. The owner of an online edition or blog can be given a warning that the publication of unsuitable materials may lead to his edition getting blacklisted, and he will lose his audience, advertisers and therefore revenue. Under coercion he won't publish what he's thinking, he won't tell what he's supposed to.
Censorship is pervasive. If you don't stand up to it from the very beginning, it can ruin you. But if every person has the awareness and skill to get around censorship, it will be rendered useless both as a restraining tool and means of exertion.
What you will be learned
You will learn:
- How to stay anonymous online
- How to prevent cyber spying
- How to protect your data
Theory and practice
While reading, you get a firm grasp on the theory: how malicious software is designed and functions, how to detect it and protect yourself from it, as well as how malicious software resists detection and removal.
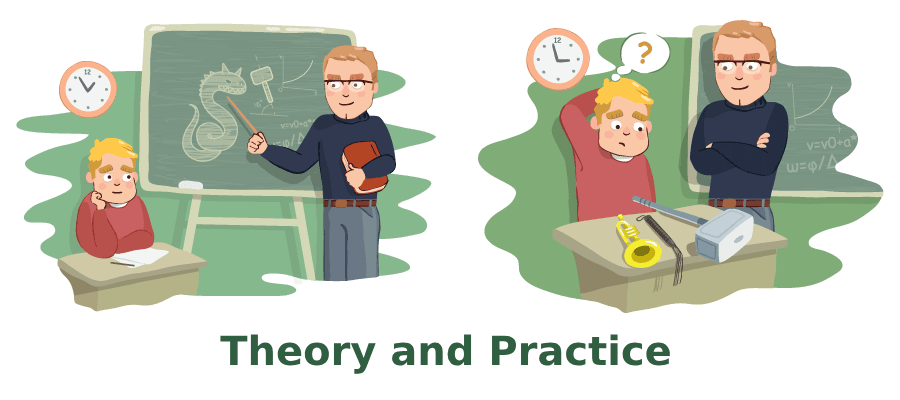
You also learn how to choose the tools for fighting malicious software, including the sandbox, traffic analysis, the system of launched process analysis, open port audit, rootkit search, signature, behavior analysis and other necessary solutions. You will need to prepare an infrastructure for your fieldwork: detection, examination and elimination of malicious software.
Alternative or similar resources
Channels listed below available only in Telegram and only in Russian.
SWAP
SWAP filled with very high quality and interesting content. Articles are published every day and are available on Telegraph. Here you can find reading starting from psychology up to professional techniques used for hacking and security audits.
The information is published for the purpose of acquaintance, and not for provocation of illegal actions.Stay on the bright side!
ⒹⒶⓇⓀⓃⒺⓉ
Time to time Darknet has some interesting articles to read. Here you can find information about vulnerabilities, cognitive information and some suspicious information about dubious earnings on the Internet. We highly recommend avoiding such earnings schemes.
XAKEP
XAKERU is quite a suspicious resource. There are a lot of hack-oriented articles published. Also they publish many articles about illegal earnings and even offer online courses. We would recommend that you either avoid this channel at all or be extremely careful if you read it for informational purposes.
TL;DR: Conclusion
If you want to stay up to date with latest publications, you can join CyberYozh Telegram channel. They post the information about new materials there, and this notification method could be quite convenient for you.


