Undoubtedly, this age of massive data breaches and gross invasions of privacy: from governments passing laws that allow spying on innocent citizens to social media breaches influencing significant elections, cyber insecurity just keeps growing.
The situation is so bad that a while ago, billionaire Warren Buffett noted that cyber-attacks were the biggest threat to humanity, bigger even than nuclear weapons.
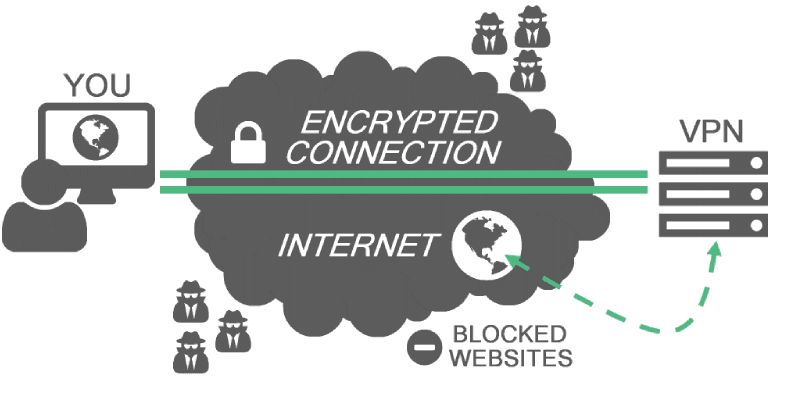
Whether you agree or you don't, the fact remains that digital security is a foremost concern among both individuals and businesses. To mitigate or avoid cyber attacks, it is crucial that you make a Virtual Private Network (VPN) an essential component of your overall digital security strategy. Identifying which VPN protocol you should use is a good initial step.
1. Point-to-Point Tunneling Protocol (PPTP)
PPTP is one of the original VPN protocols. It was first launched in the 90s by Microsoft to help people to work remotely while on a secure network. It is easy to set-up, and it has close to a hundred percent universal support.
PPTP is incredibly fast, especially when you compare it with the more modern protocols. However, it is crucial to note that modern protocols were largely developed to deal with the weaknesses of PPTP.
One of these weaknesses is that it has little to no encryption. As a result, it cannot keep a determined hacker out of your system.
When should you use PPTP?
As a security or privacy protocol, PPTP will be of no help. However, if the main reason you need a VPN is to unlock geo-restricted content, then this is the protocol for you. Also, if speed is important to you, for applications such as streaming, then PPTP is still the best protocol for you.
2. Layer 2 Tunneling Protocol/Internet Protocol Security (L2TP/IPsec)
L2TP came after PPTP, and on its own, it is quite similar to PPTP in that it is a tunneling protocol that lacks any security features. However, when paired with IPsec, which is purely a security protocol, then it can encrypt data packets with incredibly strong encryption levels.
L2TP/IPsec uses the 256-bit AES encryption standard which cannot be brute force cracked by any existing computer technology.
L2TP is also easy to set up, and it is supported by a large number of clients and services. When L2TP is bundled up with IPsec, it loses some of its connection speed advantages. Also, the protocol only uses a small number of connection/network ports, and as a result, it is easy to block.
When should you use L2TP/IPsec?
The protocol is ideal for an average internet user whose only concern is decent performance, compatibility, and a good level security.
3. OpenVPN
OpenVPN is a VPN protocol that uses OpenSSL and TLS. In addition to these two, OpenVPN uses a host of other security technologies such as SHA (Secure Hash Algorithm) for authentication.
The protocol is open-source, which means users can study, change, and distribute it as they wish. Due to the open-source nature, OpenVPN is constantly evolving, and it keeps pace with the vastly changing cybersecurity world.
OpenVPN lacks native support for a singular operating system, which means it is compatible with any system via a third-party VPN client. OpenVPN performs incredibly well on a range of User Datagram Ports (UDP) ports, but it also operates over Transmission Control Protocol (TCP) port 443.
The TCP port is the one that allows a user to piggyback on HTTPS traffic, and as a result, the protocol easily avoids port-based VPN blocking.
When should you use OpenVPN?
OpenVPN is the most secure and flexible protocol available today. Therefore, it is the go-to VPN protocol irrespective of whether you want speed or privacy. Experts agree that it is the standard when it comes to VPN protocols.
TL;DR: Conclusion
There you have it, a VPN protocol comparison of the most popular VPN protocols available today. Note that in addition to these three, there is also another popular one known as Secure Socket Tunneling Protocol (SSTP).
However, SSTP is pretty similar to OpenVPN with the only difference being that it was developed by Microsoft and is proprietary software licensed to Microsoft. As a result, there is a limit on the number of systems that are compatible with SSTP.



